- Pro
- Security
KadNap is being used against Asus routers
When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
 (Image credit: Getty Images)
(Image credit: Getty Images)
- Copy link
- X
- Threads
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Contact me with news and offers from other Future brands Receive email from us on behalf of our trusted partners or sponsors By submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.You are now subscribed
Your newsletter sign-up was successful
An account already exists for this email address, please log in. Subscribe to our newsletter- New KadNap malware infects 14,000+ routers
- Botnet uses custom Kademlia DHT protocol for resilience
- Proxy network Doppelgänger already active in the wild
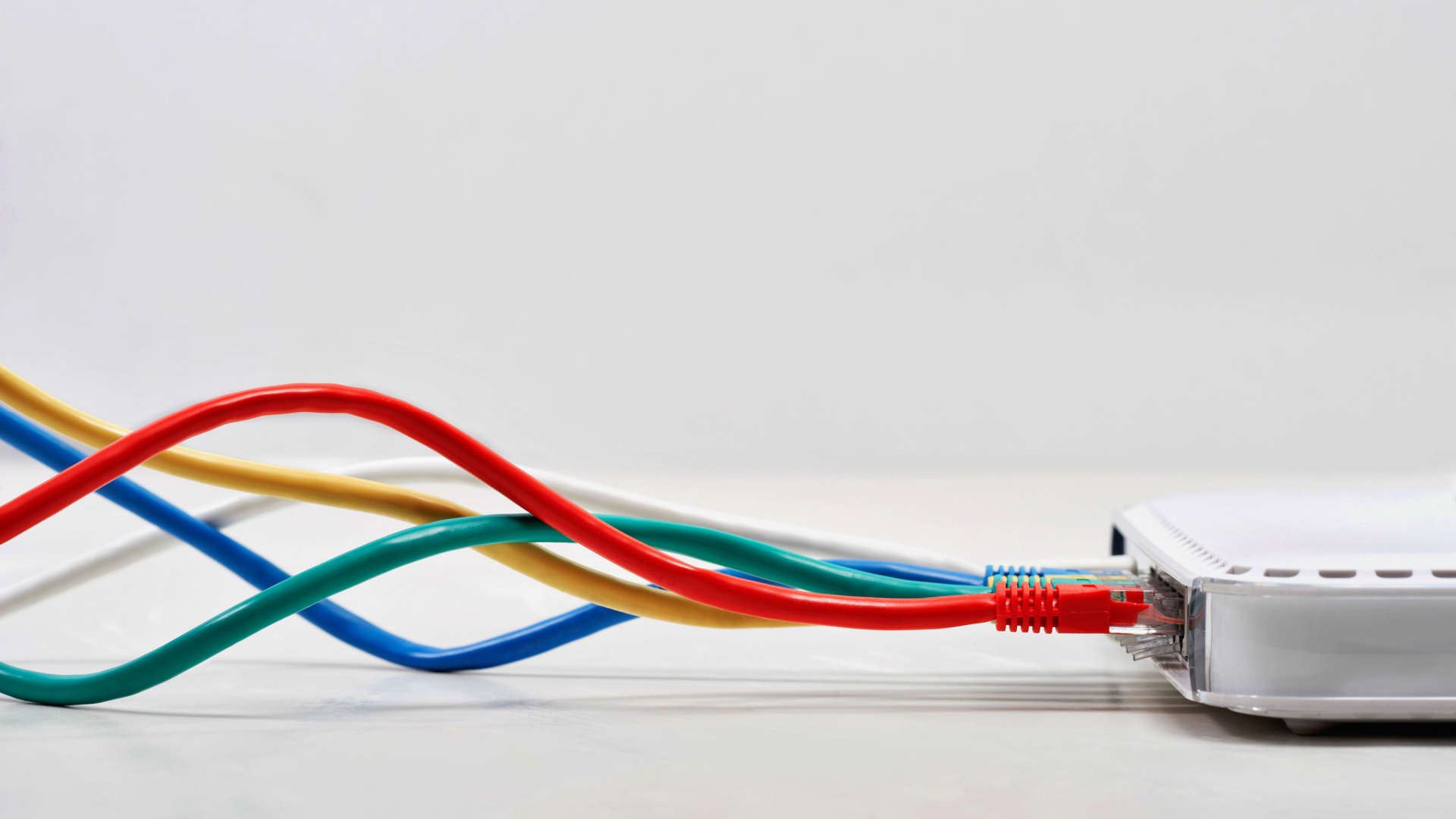
A new malware strain has been found assimilating Asus routers into a botnet for malicious proxy traffic.
Security researchers Black Lotus spotted the new network, named KadNap, and warned that in less than a year it has managed to infect more than 14,000 devices, mostly made by Asus.
The attackers don’t seem to be targeting that manufacturer specifically, so it may be the case these products are relatively easy to compromise, or there are plenty of vulnerable devices out there, compared to competing endpoints. The majority of the victims (60%) are located in the US. The remaining 40% are split between Taiwan, Hong Kong, Russia, the UK, Australia, Brazil, France, Italy, and Spain.
Article continues below You may like-
 A dangerous new Android backdoor has been found - Keenadu lurks in firmware, here's what we know
A dangerous new Android backdoor has been found - Keenadu lurks in firmware, here's what we know
-
 A massive new DDoS botnet has already snared 1.8 million devices - here's what we know about Kimwolf
A massive new DDoS botnet has already snared 1.8 million devices - here's what we know about Kimwolf
-
 This critical severity flaw in D-Link DSL gateway devices could allow for remote code execution
This critical severity flaw in D-Link DSL gateway devices could allow for remote code execution
EDR killer
What makes this botnet unique is the use of the Kademlia Distributed Hash Table (DHT) protocol, a P2P network protocol used to store and find data across a decentralized network.
Instead of relying on a central server, millions of computers cooperate to locate files and information, making it quite resilient against possible law enforcement disruption efforts.
"KadNap employs a custom version of the Kademlia Distributed Hash Table (DHT) protocol, which is used to conceal the IP address of their infrastructure within a peer-to-peer system to evade traditional network monitoring," Black Lotus said in its report.
“The innovative use of the DHT protocol allows the malware to establish robust communication channels that are difficult to disrupt, by hiding in the noise of legitimate peer-to-peer traffic," they added.
Are you a pro? Subscribe to our newsletterContact me with news and offers from other Future brandsReceive email from us on behalf of our trusted partners or sponsorsBy submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.KatNap is apparently used to build a proxy network called Doppelgänger which seems to be a rebrand of a previous network called Faceless. This one, the researchers say, was built using TheMoon malware.
The botnet is past the construction stage, since it is apparently already being used in the wild.
Via The Hacker News
 The best antivirus for all budgetsOur top picks, based on real-world testing and comparisons
The best antivirus for all budgetsOur top picks, based on real-world testing and comparisons➡️ Read our full guide to the best antivirus1. Best overall:Bitdefender Total Security2. Best for families:Norton 360 with LifeLock3. Best for mobile:McAfee Mobile Security
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.
Sead FadilpašićSocial Links NavigationSead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.
View MoreYou must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.
Logout Read more A dangerous new Android backdoor has been found - Keenadu lurks in firmware, here's what we know
A dangerous new Android backdoor has been found - Keenadu lurks in firmware, here's what we know
 A massive new DDoS botnet has already snared 1.8 million devices - here's what we know about Kimwolf
A massive new DDoS botnet has already snared 1.8 million devices - here's what we know about Kimwolf
 This critical severity flaw in D-Link DSL gateway devices could allow for remote code execution
This critical severity flaw in D-Link DSL gateway devices could allow for remote code execution
 NGINX servers hijacked in global campaign to redirect traffic
NGINX servers hijacked in global campaign to redirect traffic
 CISA reveals warning on Asus software flaw, here's what you need to do to stay safe
CISA reveals warning on Asus software flaw, here's what you need to do to stay safe
 Dangerous WebRAT malware now being spread by GitHub repositories
Latest in Security
Dangerous WebRAT malware now being spread by GitHub repositories
Latest in Security
 Hackers hijack WordPress sites to spread malware using fake CAPTCHA
Hackers hijack WordPress sites to spread malware using fake CAPTCHA
 This 'fascinating' Microsoft Excel security flaw teams up spreadsheets and Copilot Agent to steal data
This 'fascinating' Microsoft Excel security flaw teams up spreadsheets and Copilot Agent to steal data
 HPE warns of dangerous security flaw which could allow Aruba OS password resets
HPE warns of dangerous security flaw which could allow Aruba OS password resets
 Russian hackers target HR departments with vicious new 'BlackSanta' malware
Russian hackers target HR departments with vicious new 'BlackSanta' malware
 ‘These actions are unprecedented and unlawful’: Anthropic sues Pentagon over “supply chain risk” designation — claims free speech and due process violations
‘These actions are unprecedented and unlawful’: Anthropic sues Pentagon over “supply chain risk” designation — claims free speech and due process violations
 Watch out Microsoft Teams users - hackers are spreading a dangerous new phishing scam, here's what we know
Latest in News
Watch out Microsoft Teams users - hackers are spreading a dangerous new phishing scam, here's what we know
Latest in News
 Quordle hints and answers for Thursday, March 12 (game #1508)
Quordle hints and answers for Thursday, March 12 (game #1508)
 NYT Strands hints and answers for Thursday, March 12 (game #739)
NYT Strands hints and answers for Thursday, March 12 (game #739)
 NYT Connections hints and answers for Thursday, March 12 (game #1005)
NYT Connections hints and answers for Thursday, March 12 (game #1005)
 Intel's new Core Ultra 200S Plus CPUs promise a big boost for PC gamers
Intel's new Core Ultra 200S Plus CPUs promise a big boost for PC gamers
 How to watch Sunny Nights on TVNZ+ (it's *FREE*)
How to watch Sunny Nights on TVNZ+ (it's *FREE*)
 Why does the MacBook Air M5 keyboard look different? Blame your iPhone
LATEST ARTICLES
Why does the MacBook Air M5 keyboard look different? Blame your iPhone
LATEST ARTICLES- 1Meta’s Moltbook deal means social media will fill with even more bots talking to each other
- 2Nintendo Virtual Boy review: don’t buy this awful Nintendo Switch 2 add-on
- 3OpenAI reportedly building a GitHub alternative after saying Microsoft-owned platform is 'not yet meeting our expectations'
- 4Burson's Stellar headphone amps promise head-fi heaven in spacecraft-inspired Star Wars style
- 5'Creating a fully keyboard-accessible site...isn’t free; it requires a lot of work and knowledge': Microsoft is making it easier to build complex websites without a mouse